Publishing documentation is yet another task on the long list of things to do as a library author. I had an idea – what if that was just done automatically once you push your package to Nuget.org? That’s why I created NuDoc.NET. With C# we got XML comments that are in the code which makes… Continue reading NuDoc.NET in Preview
.NET TargetFramework and Dependencies
Recently I’ve had reasons to dive deep into how .NET does dependency resolution. In a real world application with transitive dependencies the same package can be referenced for multiple reasons. To make things more complex, the dependencies of a .NET assembly are specified per target framework. It turns out that this can create a situation… Continue reading .NET TargetFramework and Dependencies
Entity Framework Core and Private Properties
Object oriented design is all about encapsulation. A class provides methods to manipulate its data and only allows manipulation that keeps the objects’ state correct. That works fine in theory, but in real life objects need to be loaded/materialized from a database and this usually means that property setters must be public. But not with… Continue reading Entity Framework Core and Private Properties
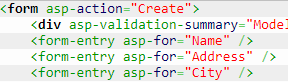
A form-entry Tag Helper
Writing line of business applications usually means creating a lot of forms for data entry. Writing the HTML for them over and over again is tedious and also means copy-pasting the layout structure into every single form. Copy-pasting works fine as long as we one is happy with the design, but when it needs to… Continue reading A form-entry Tag Helper
Renaming Kentor.AuthServices Nuget packages to Sustainsys.Saml2
Last year I left Kentor for new adventures as an independent consultant. I got the Kentor.AuthServices project with me, but of course need to rename it as it is not associated with Kentor any more. So how does one rename a library and nuget packges with 100k+ downloads and users all over the world? Simply… Continue reading Renaming Kentor.AuthServices Nuget packages to Sustainsys.Saml2