Last year I left Kentor for new adventures as an independent consultant. I got the Kentor.AuthServices project with me, but of course need to rename it as it is not associated with Kentor any more. So how does one rename a library and nuget packges with 100k+ downloads and users all over the world? Simply… Continue reading Renaming Kentor.AuthServices Nuget packages to Sustainsys.Saml2
Tag: Kentor.AuthServices
Going Independent
After more than 8 years at Kentor the time as come to move on. I’m leaving Kentor and starting my own business. I will continue to work with identity and access management, especially SAML2 on .NET. I will do consulting, open source development and training, both on site and remotely. The Kentor.AuthServices project will be… Continue reading Going Independent
Kentor.AuthServices 0.21.2 Security Release
Kentor.AuthServices 0.21.2 has just been released to NuGet. It is a security release fixing three issues. XML External Entity Injection (affecting .NET 4.5 only) Malicious IdP can cause write to arbitrary file Flawed ReturnUrl validation leads to Open Redirect The first two issues were reported by John Heasman, Morgan Roman and Joshua Estalilla from DocuSign.… Continue reading Kentor.AuthServices 0.21.2 Security Release
Kentor.AuthServices v0.20.0 Released
Half a years worth of pull requests with great features have finally been baked into an official release of Kentor.AuthServices which is now available on Nuget. The most important fixes are improved active/passive handling for the Owin middleware and full support for SHA256/384/512 as it is time to leave SHA1. First of all I would… Continue reading Kentor.AuthServices v0.20.0 Released
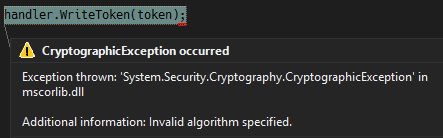
Why Enabling SHA256 Support for XML Signatures Breaks JWT Signing
For some times there’s been bug reports to Kentor.AuthServices, IdentityServer3 and System.IdentityModel.Tokens.Jwt about enabling SHA256 XML signature support sometimes breaks JWT signing. It fails with an error of System.Security.Cryptography.CryptographicException: Invalid algorithm specified. This has been one of those annoying bugs where everyone’s solution works perfectly by itself, but combined they fail. I closed this issue… Continue reading Why Enabling SHA256 Support for XML Signatures Breaks JWT Signing