Kentor.AuthServices 0.21.2 has just been released to NuGet. It is a security release fixing three issues. XML External Entity Injection (affecting .NET 4.5 only) Malicious IdP can cause write to arbitrary file Flawed ReturnUrl validation leads to Open Redirect The first two issues were reported by John Heasman, Morgan Roman and Joshua Estalilla from DocuSign.… Continue reading Kentor.AuthServices 0.21.2 Security Release
Tag: Security
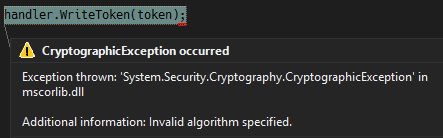
Why Enabling SHA256 Support for XML Signatures Breaks JWT Signing
For some times there’s been bug reports to Kentor.AuthServices, IdentityServer3 and System.IdentityModel.Tokens.Jwt about enabling SHA256 XML signature support sometimes breaks JWT signing. It fails with an error of System.Security.Cryptography.CryptographicException: Invalid algorithm specified. This has been one of those annoying bugs where everyone’s solution works perfectly by itself, but combined they fail. I closed this issue… Continue reading Why Enabling SHA256 Support for XML Signatures Breaks JWT Signing
Kentor.AuthServices 0.18.1 Breaking Changes
Today we released Kentor.AuthServices 0.18.1. It contains a number of bug fixes, but also a couple of breaking changes to a mostly internal API and logout handling. You are affected if… you build a HttpRequestData yourself, instead of using a build in ToHttpRequestData() extension method. you are using Single Logout and… you have a ClaimsAuthenticationManager… Continue reading Kentor.AuthServices 0.18.1 Breaking Changes
Breaking Changes to SignedXml in MS16-035
Earlier this month, Microsoft released MS16-035 that addresses issues I previously reported in SignedXml. They did not only fix the duplicate Id vulnerability I reported though, they also fixed a number of other issues – introducing some breaking changes. This post is an effort to document those and changes and the registry switches that can… Continue reading Breaking Changes to SignedXml in MS16-035
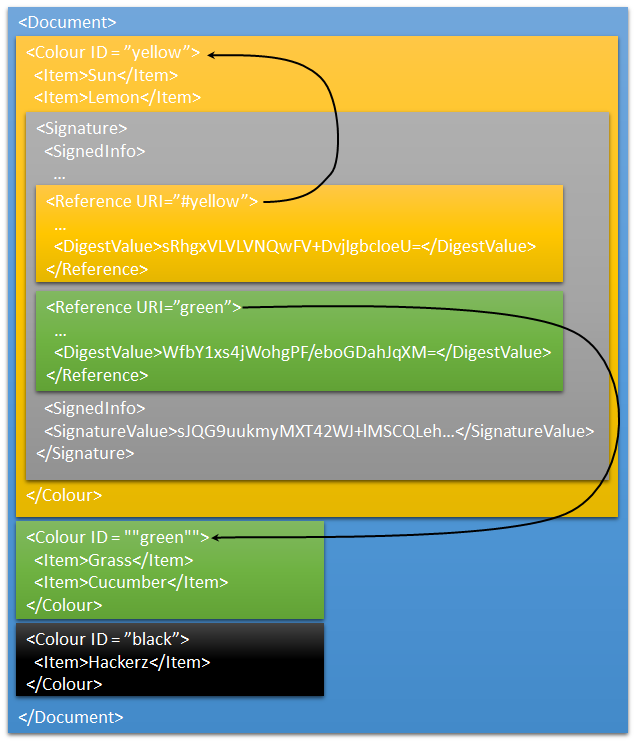
Vulnerability in .NET SignedXml
.NET’s SignedXML class has had a risky implementation for lookup of XML elements by id in GetIdElement() when resolving signed xml references. The lookup validated only the first element if there are several with the same id. This opens up for XML Signature Wrapping attacks in any library that is using the default implementation without… Continue reading Vulnerability in .NET SignedXml