Publishing documentation is yet another task on the long list of things to do as a library author. I had an idea – what if that was just done automatically once you push your package to Nuget.org? That’s why I created NuDoc.NET. With C# we got XML comments that are in the code which makes… Continue reading NuDoc.NET in Preview
Category: Web
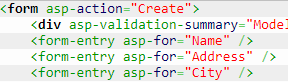
A form-entry Tag Helper
Writing line of business applications usually means creating a lot of forms for data entry. Writing the HTML for them over and over again is tedious and also means copy-pasting the layout structure into every single form. Copy-pasting works fine as long as we one is happy with the design, but when it needs to… Continue reading A form-entry Tag Helper
Kentor.AuthServices 0.21.2 Security Release
Kentor.AuthServices 0.21.2 has just been released to NuGet. It is a security release fixing three issues. XML External Entity Injection (affecting .NET 4.5 only) Malicious IdP can cause write to arbitrary file Flawed ReturnUrl validation leads to Open Redirect The first two issues were reported by John Heasman, Morgan Roman and Joshua Estalilla from DocuSign.… Continue reading Kentor.AuthServices 0.21.2 Security Release
Kentor.AuthServices v0.20.0 Released
Half a years worth of pull requests with great features have finally been baked into an official release of Kentor.AuthServices which is now available on Nuget. The most important fixes are improved active/passive handling for the Owin middleware and full support for SHA256/384/512 as it is time to leave SHA1. First of all I would… Continue reading Kentor.AuthServices v0.20.0 Released
Kentor.AuthServices 0.18.1 Breaking Changes
Today we released Kentor.AuthServices 0.18.1. It contains a number of bug fixes, but also a couple of breaking changes to a mostly internal API and logout handling. You are affected if… you build a HttpRequestData yourself, instead of using a build in ToHttpRequestData() extension method. you are using Single Logout and… you have a ClaimsAuthenticationManager… Continue reading Kentor.AuthServices 0.18.1 Breaking Changes